Configure Rift
The following steps configure the connection between a Tecton Account and the Customer Data Plane AWS resources. See the Virtual Private Tecton Architecture overview for more information on the Customer Control Plane.
Before you get started:
- Decide on a name for your deployment (e.g.
mycompany-production). This name will become part of the URL that is used to access your Tecton UI (mycompany-production.tecton.ai). Note: This name must be less than 22 characters. - Determine which AWS region you'd like Tecton deployed into (e.g.
us-west-2).
Configuring AWS resources
If your organization uses Terraform to manage AWS resources, we recommend you leverage this sample terraform setup repository in place of manually entering these values. The instructions below may still be a valuable reference when adapting the template to your needs.
At the end of these steps, you will have created:
- A S3 Bucket where Tecton will write feature data.
- The cross-account role for the Tecton control plane to manage DynamoDB and
S3, e.g.
tecton-{DEPLOYMENT_NAME}-cross-account-roleandtecton-{DEPLOYMENT_NAME}-cross-account-policy.
Create a Tecton S3 Bucket
Tecton will use a single S3 bucket to store all of your offline materialized feature data.
To set this up,
create an S3 bucket
called tecton-[DEPLOYMENT_NAME] (e.g. tecton-mycompany-production).
-
Ensure the bucket's region is the same as the region in which you'd like to deploy Tecton (e.g.
us-west-2) -
Enable default encryption using the Amazon S3 key (SSE-S3)
-
Add a Policy to the S3 bucket
tecton-{DEPLOYMENT_NAME}to allow Tecton to read/write to it.-
Navigate to S3 ->
tecton-{DEPLOYMENT_NAME}S3 Bucket -> Permissions. There, add the following policy, replacing{TECTON_CONTROL_PLANE_ARN}with the ARN of the Tecton Control Plane account. Ask your Tecton Account Manager if you do not have this ARN.{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "TectonS3",
"Effect": "Allow",
"Principal": {
"AWS": "{TECTON_CONTROL_PLANE_ARN}"
},
"Action": ["s3:GetObject", "s3:PutObject", "s3:DeleteObject"],
"Resource": "arn:aws:s3:::tecton-{DEPLOYMENT_NAME}/*"
},
{
"Sid": "TectonS3List",
"Effect": "Allow",
"Principal": {
"AWS": "{TECTON_CONTROL_PLANE_ARN}"
},
"Action": "s3:ListBucket",
"Resource": "arn:aws:s3:::tecton-{DEPLOYMENT_NAME}"
}
]
} -
Make sure the Object Ownership Setting for the
tecton-{DEPLOYMENT_NAME}S3 Bucket is set to ACLs Disabled (Bucket Owner Enforced). This allows the AWS account with the S3 bucket to automatically own and have full control over objects written by Rift.- In the AWS console open the S3 bucket configuration for the
tecton-${DEPLOYMENT_NAME}bucket - Navigate to the permissions tab (if not already there)
- Under the Edit Object Ownership section, click the Edit button
- Select ACLs disabled (recommended)
- This should change Object Ownership to Bucket owner enforced
- Click Save Changes
- In the AWS console open the S3 bucket configuration for the
-
Create a cross-account role for the Tecton Control Plane
Next, you'll need to create an access policy and an IAM role which the Tecton control plane will use to orchestrate AWS resources in your account.
-
In the AWS Console of the account you want to deploy Tecton into, go to the IAM service.
-
Click the Policies tab in the sidebar.
-
Click Create Policy.
-
Paste in the following JSON policy, replacing
${REGION}with the AWS region you selected for your deployment,${ACCOUNT}with the account ID of your AWS account,${DEPLOYMENT_NAME}with your Tecton deployment name.https://github.com/tecton-ai/tecton-terraform-setup/blob/master/templates/rift_ca_policy.json -
Click Next: Tags
-
Add the following tag to the policy
key: tecton-accessible:DEPLOYMENT_NAME
value: true -
Click Next: Review
-
Give the policy an easy to remember name starting with
tecton-, liketecton-{DEPLOYMENT_NAME}-cross-account-policy -
Click Create Policy
-
-
Click the Roles tab in the sidebar.
-
Click Create role.
-
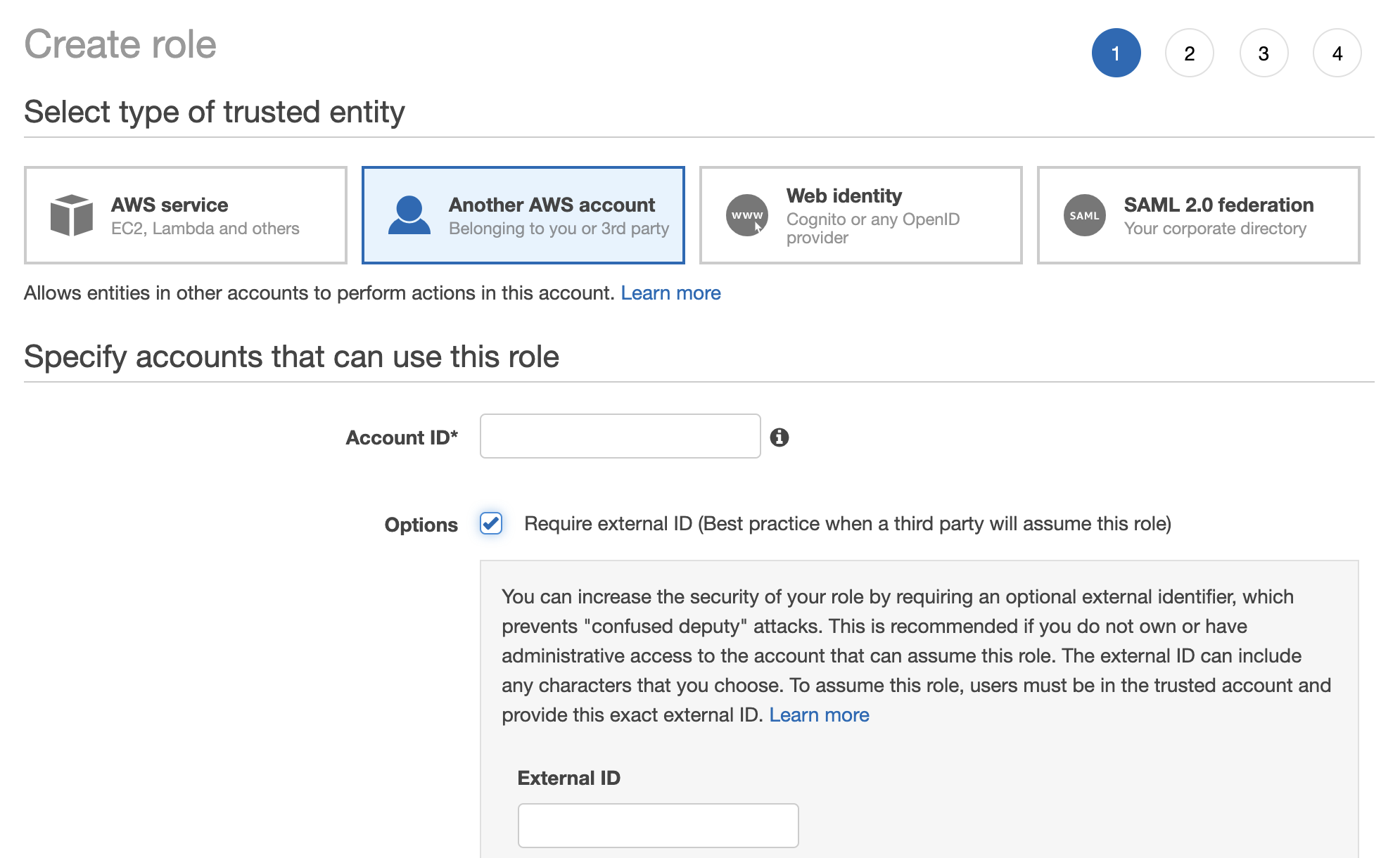
Under Select type of trusted entity, click the Another AWS account tile.
-
Specify Tecton's Account ID. Please contact your Account Manager to get the appropriate ID.
-
Enable the option "Require external ID."
-
Enter a random External ID of your choice (for example, a UUID works well). Make sure to note down the external ID that you choose -- you'll need to provide this to Tecton to complete the installation.
-
Click the Next: Permissions button
-
Search for the policy you just created (e.g.
tecton-{DEPLOYMENT_NAME}-cross-account-policy), and click the check box next to that policy to attach the policy to the new role. -
Click the Next: Tags button.
-
Click the Next: Review button.
-
In the Role name field, enter a role name starting with
tecton-, such astecton-{DEPLOYMENT_NAME}-cross-account-role. -
Click Create role. You will see a list of roles displayed.
-
Notify the Tecton team
Once you've completed the above setup, notify Tecton that you are ready to connect to AWS resources in your account.
Please include the following information: the ARN and External ID of the role you created for the Tecton control plane.